
EMLogics develops outstanding software solutions that provide value to your organization. We will go from a requirement — or an idea — to prototype to implementation. Your application will be tested to ensure all functionality requirements are met. Exceeding your expectations is our upmost priority.
From designing your website, internal, or external applications, we can take care of it — from the initial stages through production support.
We design our icons, color pallets, business cards, company letter head, and mailing envelopes. It's all done in house and we extend that benefit to you. We will go through multiple interactions until you are satisfied with the final product/service that truly reflects your brand.
Since time saving is so valuable to you, when you need to update your digital assets, you will find them all in one place — readily accessible and adaptable to your applications.

Traditionally, businesses need to have a room with servers, switches, and all sorts of devices to run their applications. Apart from that aging infrastructure, you might use legacy software that does not provide value to your operations, even when it is updated.
Most canned solutions are like that — a "one solution fits all" mentality. They were created to maximize profits and not with the customer in mind. We take a different path by putting you first every step of the way. From creating integrations with third party api providers, to using S3 to store files securely in the cloud, to scalable databases that meet your demands. All without you having expensive equipment to keep track of and maintain.
We take security very seriously. It is not an after thought. Right when we start building your application, we strategize the most feasible security flow we can implement following industry guidelines and best practices.
Not long ago, dual factor authentication was out of reach to small businesses and only available to large corporations. Thanks to open source technology, this extremely important security feature is cost effective to implement. That is the reason that for the majority of our applications, we recommend this two factor/dual factor authentication mechanism and discourage the use of sending code through SMS messages. While other developers consider this feature an upgrade, we include it with your applications by default.


Even though many details have to be taken care of, we provide an easy way to "glance" at the whole picture; an intuitive interface that allows you to quickly zoom into your focus area. For instance, a friendly navigation with an easy to follow flow provides a pleasant experience when filling out long forms. Did we mention that the user does not have to provide redundant information?
Filling out a multiform with smart navigation

The information you create, is only protected from regular access. This type of protection is minimal and does not provide confidentiality since it is readable by those with access to the database. It is fine to use if there are no personal information protection requirements.

The information is encrypted using Advanced Encryption Standard (AES) before being stored. Your encryption key is encrypted with a master key that is not stored in the database. This adds a layer of protection in order to comply with regulations.


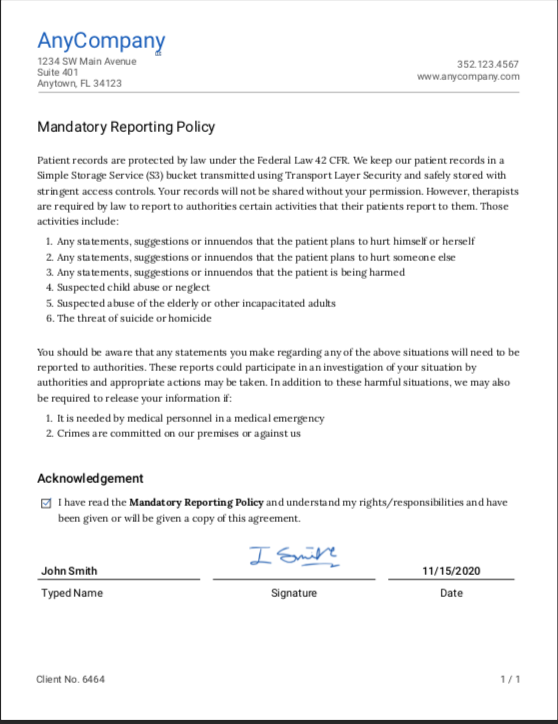
The customer should not have a fillable pdf that must be downloaded, filled in, emailed back, scanned, and then have the data typed into a spreadsheet or a database. If a form needs to be updated, recreating the pdf can be cumbersome.

Sign the form online (with the mouse, pencil, or a finger). The data is entered automatically into a database and the documents are securely stored. Of course, the customer gets a copy online — all without leaving the application.

You have to send invoices to your customers through mail, they have to call and pay over the phone, or visit a third party website to make a payment. Too complicated for all.

Just send a secure link to your customer and they will be able to pay with Apple Pay, Google Pay, credit card, debit card, or check. No need to mail any invoice. It's that simple.


You have to open a client email or go to a third party provider and choose the template, paste the client address, and make edits as appropriate. This work flow interruption is treated as a continuous task flow.

Perform your routine tasks and let the system take care of sending the emails without you having to get involved. Use your time to add value to your activities. Make the system work for you, rather than you work for the system.

Complexity is easy to add to a process or a product. Simplicity, however, is difficult to achieve as more features or requirements are introduced. Our approach is to keep things simple, consistent, and documented. Because of this, we are able to evolve your application over time without the need for costly redesign overhaul.
Application with dashboard showing real time data.
We chose open source for its many benefits. The code is created/updated and reviewed by numerous people. The shear number of ideas allow the creation of code that can scaled and be modified (forked) for different purposes without restrictions (always check the license). Software vulnerabilities are discovered and made public on the internet, allowing contributors to fix the issues.
Open software allows the creation of applications and solutions without having to start from scratch. That is the reason we run our business using it and we encourage our customers to do the same.

A React Server side rendering framework to build applications that are SEO friendly with minimal configuration

Used to create the user interface where components are shared by multiple screens without replication

JavaScript on the server, handles data from and to the client. It also manages API routes and responses

Creates programming tasks from imaging processing to document management and beyond

A modern general purpose language used to develop iOS mobile and MacOS desktop applications

A relational database for handling normalized as well as json data with first class features and security
We get to be creative in developing new solutions or improve existing ones. We cannot wait to provide you with exceptional service!
Contact us